Uncovery
Attack surface mapping and control
Uncovery is a 100% automated module that gives you complete visibility over Internet assets and their level of risk. Non-intrusive, it works simply from a domain name or an IP address.
Discover my attack surface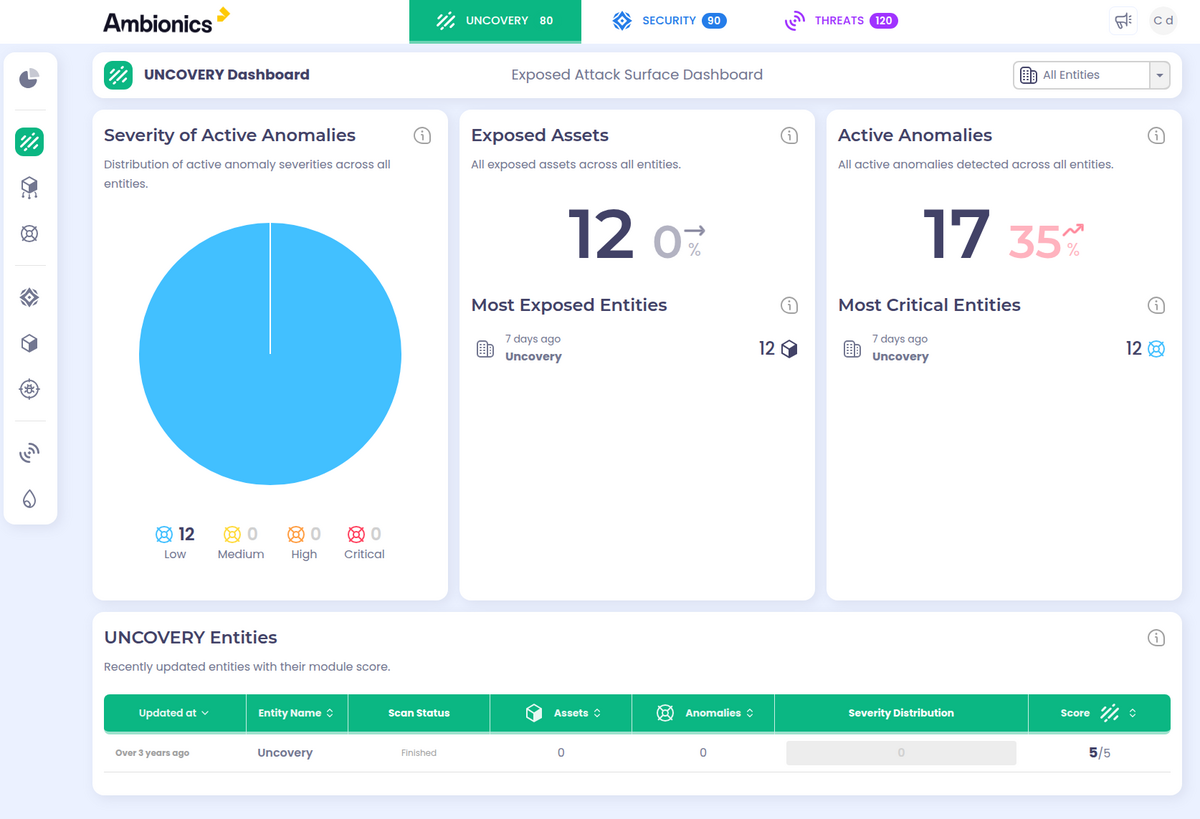
Key Features
Asset Discovery
Continuous identification of all your Internet assets (IPs, domains, subdomains).
Shadow IT Detection
Spot test environments, subsidiaries, or servers forgotten by your teams.
Dynamic Inventory
An always up-to-date database of your attack surface in real time.
Continuous Discovery
Integrated Analysis Agents
The Uncovery module enables rapid identification of security risks through a combination of complementary analysis modules ensuring qualified, weighted and time-tracked vulnerability reporting.
Security Controller
Monitors security hygiene of exposed assets: misconfigurations, bad practices, high-risk exposures. Rules based on ANSSI recommendations and our teams' offensive expertise.
CVE Inspector
Identifies CVE vulnerabilities associated with detected technologies. Automatic conversion to CPE format for correlation with NVD and exploit-DB databases. Continuous tracking and ticket updates.
VulnScan Auditor
Active tests based on the Nuclei engine enriched with thousands of test models and exclusive Ambionics templates. Automatic triggering as soon as a critical vulnerability is published (Log4j, XORtigate...).
WebChange Profiler
Detects visual or structural changes in web pages. Pixel-by-pixel comparison to identify defacement, unplanned production deployment or malicious alteration.
Uncovery Detection Scope
- Unknown Assets (Shadow IT)
- Exposed Services
- Subdomains
- Certificates
- Technologies
- DNS
- Ports
- Technical Leaks
Uncovery's Impact
Monitored assets
Automated
Why choose this module?
Total Visibility
Leave no more blind spots in your Internet infrastructure.
Operational Agility
Deploy and monitor without agents or complex configuration.
Native Prioritization
Immediately identify which asset presents the highest risk.
See our platform in action
Request a personalized demonstration and see how this module can strengthen your security.