Threats
Monitor and anticipate emerging threats
The Threats module is a service offering that provides continuous monitoring of indirect exposure vectors: dark web, specialized forums, marketplaces, social networks and databases of compromised items.
Discover my attack surface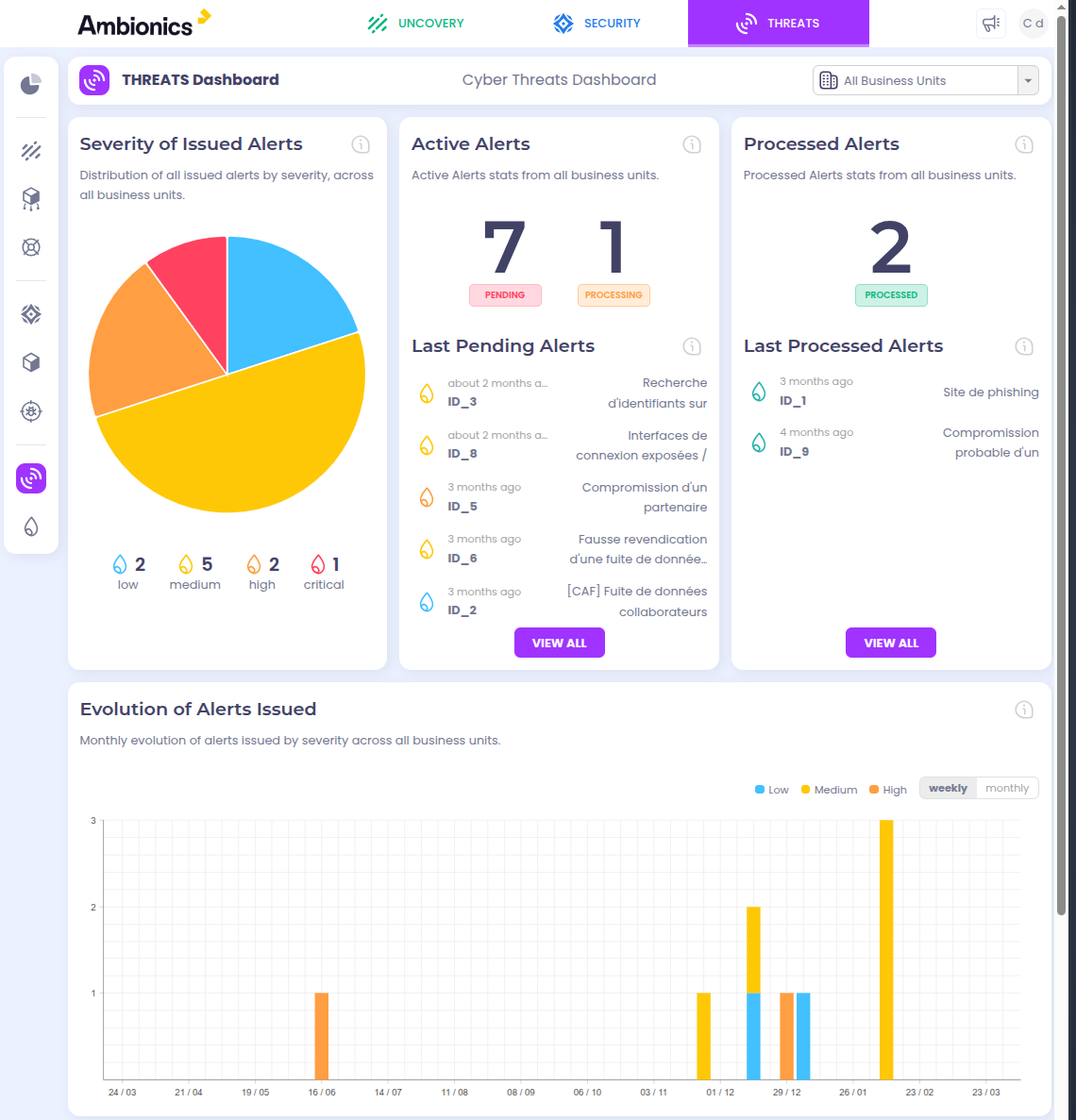
Key Features
Data leak detection
Detect leaks of sensitive data concerning your organization: confidential documents, strategic information, and customer or partner data.
Compromised credentials
Identify compromised credentials (emails, passwords) before they are exploited in targeted attacks.
Anticipating attack campaigns
Monitor weak signals and mentions of your organization to anticipate attack campaigns before they are launched.
How it works
Monitored Sources
Our CTI team continuously monitors a wide range of sources to detect threats targeting your organization.
Dark Web
Tor, I2P, cybercriminal marketplaces, private forums accessible only via anonymous networks.
Specialized Forums
Hacker communities, data resale forums, attack technique exchange spaces.
Messaging & Social Networks
Telegram, Discord, Twitter/X, private channels where malicious actors coordinate.
Compromised Databases
Leaks, breaches, combo lists, stolen credential databases and exposed data.
Detection Types
- Compromised credentials (emails, passwords, API tokens)
- Exposed confidential documents (reports, contracts, strategic data)
- Mentions of your organization (attack preparation, targeted discussions)
- Sale of access to your systems (Initial Access Brokers)
- Compromised customer or partner data
- Stealer logs (Redline, Raccoon, Vidar) exposing sessions and cookies
- Source code leaks on GitHub, GitLab and Pastebin
- Typosquatting and domain impersonation
State-of-the-art Intelligence
Active monitoring
Expert team
Why choose this module?
Analysis by CTI experts
Weak signals are analyzed by CTI experts to provide intelligence that is exploitable and immediately actionable.
Multiple sources
Monitoring of the dark web, specialized forums, marketplaces, social networks and databases of compromised items.
Actionable intelligence
No noise, no unnecessary alerts: only intelligence that is exploitable and immediately actionable to protect your organization.
See our platform in action
Request a personalized demonstration and see how this module can strengthen your security.