Security
Assess real security through continuous pentesting
Assess the real resilience of your assets through continuous penetration testing performed by experts.
Discover my attack surface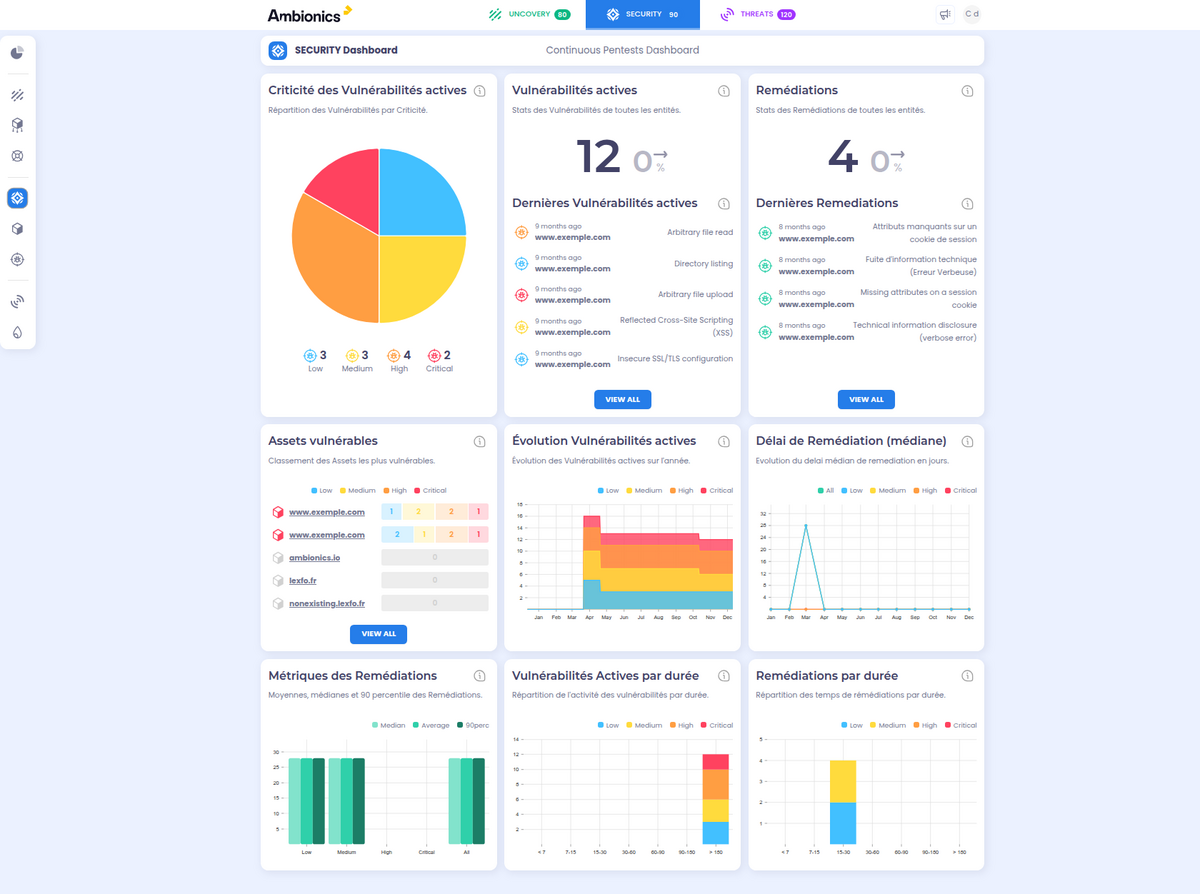
Key Features
Continuous Manual Pentest
Certified auditors test your critical assets using attacker methods.
Zero False Positives Guaranteed
Each vulnerability is manually validated before being reported to you.
Vulnerability Scanning
Vulnerability scans are run continuously across your perimeter, then qualified by our experts.
How it works
Vulnerability Lifecycle
Each vulnerability follows a rigorous workflow from detection to remediation validation, with full traceability.
Detected
Vulnerability detected and reported in a detailed record written by an expert.
Monitored
Weekly counter-audit of the vulnerability.
Fixed
Fix detected by the weekly counter-audit and manually qualified.
Verified
Active monitoring after remediation to detect any regression.
Attack Vectors & Critical Flaws
- RCE
- SQL Injection
- Authentication
- API Security
- Cloud Config
- Business Logic
- SSRF
- Information Disclosure
Offensive Excellence
Cyber experts
False positive
Why choose this module?
Enhanced Trust
Rely on concrete evidence of exploitability to decide.
On-demand Expertise
Chat live with our auditors about your vulnerabilities.
Simplified Compliance
Generate premium audit reports for your regulators and clients.
See our platform in action
Request a personalized demonstration and see how this module can strengthen your security.