Our CTEM Platform
Take control of your attack surface with a solution driven by experts
Ambionics combines three complementary modules for continuous management of your cyber exposure: asset mapping, security assessment, and threat intelligence.
From reactive security to continuous anticipation.
CTEM (Continuous Threat Exposure Management) is a 5-step strategy designed to proactively reduce your attack surface. No more static annual audits: our approach maps, tests, and prioritizes your risks continuously to focus only on real threats.
Discovery
Map assets actually exposed on the Internet.
Assessment
Validate exploitability through real offensive attacks.
Prioritization
Prioritize based on business impact and active threats.
Remediation
Support your teams and verify fixes.
Measurement
Manage the global reduction of your risk over time.
Three modules in a single solution
Ambionics unifies discovery, offensive assessment, and threat intelligence in a continuous CTEM approach.
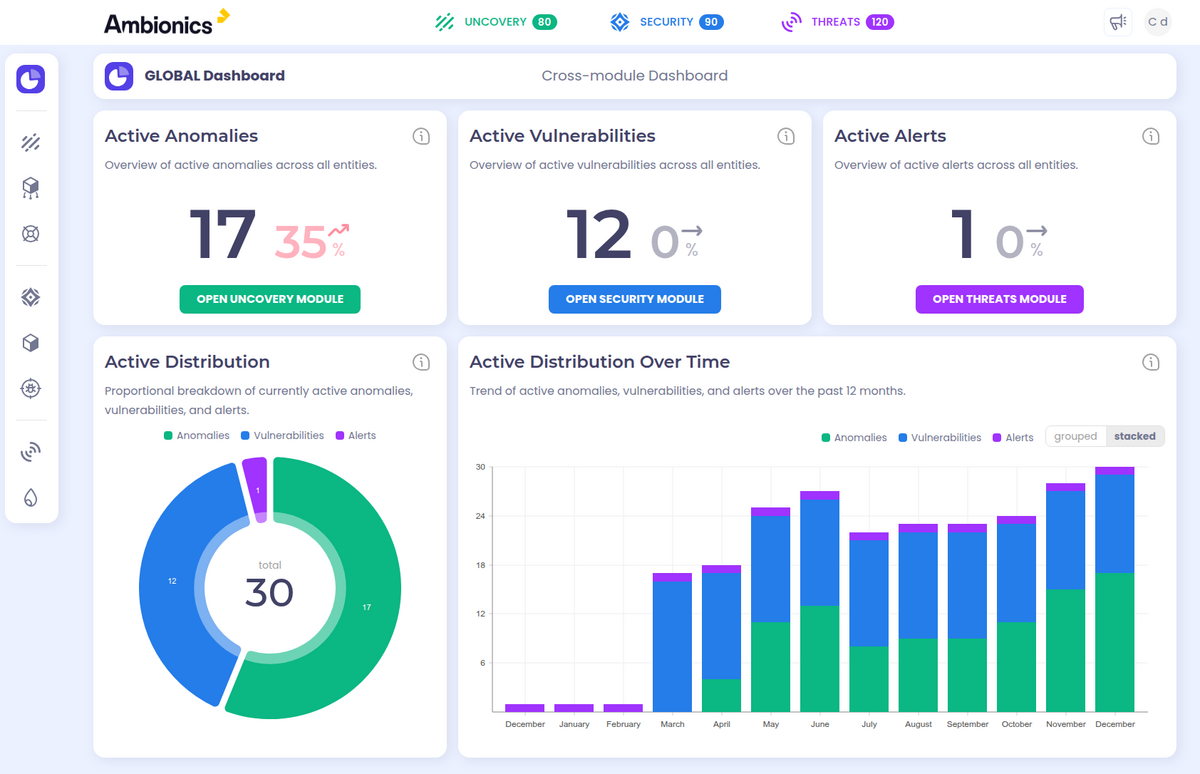
Uncovery
Attack Surface Mapping
- Automated discovery of exposed assets
- Detection of Shadow IT and forgotten environments
- Analysis agents reporting anomalies
Security
Real Security Validation
- Penetration testing by PASSI-certified experts
- Zero false positives guaranteed
- Weekly counter-audits of remediations
Threats
Threat Intelligence
- Dark web and forums monitoring
- Compromised credentials detection
- Alerts before exploitation
What our clients value most
A solution designed for every team: CISOs, CIOs, SecOps
We've combined 15 years of offensive audit expertise into a platform that gets straight to what matters: real risk reduction.
Zero False Positives
Maximum noise reduction. Every alert is manually validated by our experts before reaching you.
One-glance Vision
Manage your attack surface through an intuitive interface that provides a clear and actionable framework.
On-demand Experts
A dedicated comment space to speak directly with our auditors.
15+ Years Expertise
Benefit from the cumulative know-how of our high-level offensive security auditors.

An Integrable Platform
Ambionics natively integrates within complex and heterogeneous IT ecosystems.
REST API
Complete, documented APIs for automation and integration with your existing tools.
Multiple Exports
Exports in PDF, DOCX, CSV and Excel formats
4000+ Integrations
Connectors to over 4,000 market solutions via our integration partners.
SSO & MFA
Advanced IAM integration with single sign-on and multi-factor authentication.
Multi-Entity
Logical segmentation by entity, adapted for groups, subsidiaries and distributed organizations.
Dedicated Instance
Flexible hosting options meeting regulatory and sovereignty requirements.